Enterprise grade
security practices
At MockFlow we ensure, our infrastructure, development, data and application follow security compliance at all times

Infrastructure Security
We use top of the line services for hosting and protecting our infrastructure. MFA, key rotation, VPN and other important factors are followed at the server level
AWS
All of MockFlow is hosted with Amazon Web Services - the leader in cloud infrastructure as a Service (IaaS) as per Gartner
FireWall
MockFlow is protected with network firewall and application-level firewall along with intrusion detection and alerts.
DDOS Safeguard
Our servers are protected actively from DDOS attacks using Cloudflare. And also they are monitored every minute for any anomalies
SOC2 & ISO 27001 certified hosts
We only use SOC2 and ISO 27001 certified services for hosting customer data. This ensures our cloud providers are trustworthy
Data Protection
We protect and safeguard all customer data with the following actions
Continuous Backups
We perform continuous backup of customer data and also store them securely in different locations
Encryption of sensitive data
256-bit key is used for encrypting sensitive information like passwords
S3 File Hosting
Files are stored at AWS S3 that provides geographically-dispersed Availability Zones, protected by 99.999999999% of durability
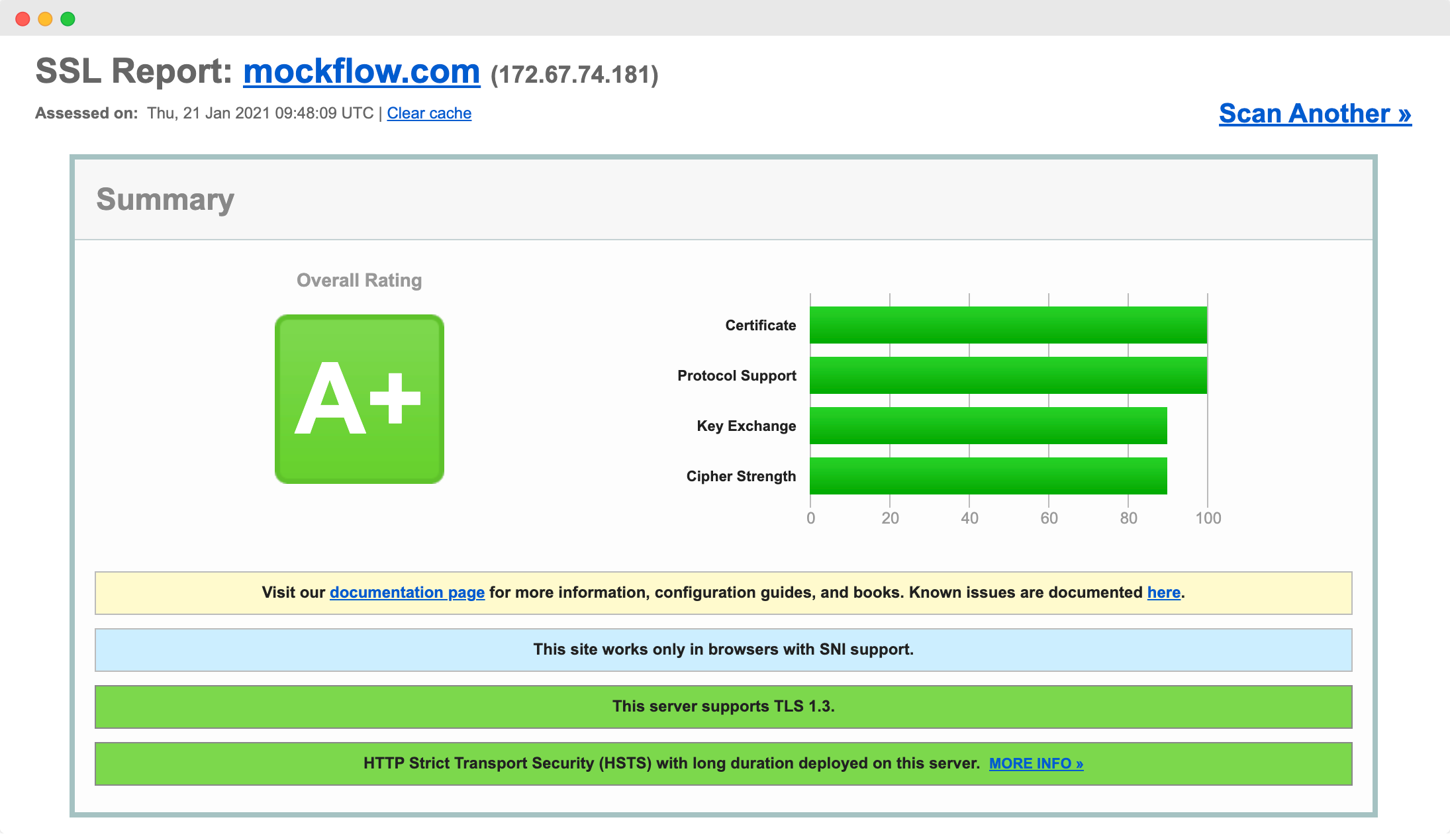
 SSL for data transmission
SSL for data transmission
Only SSL/HTTPS is used for all data transmissions protected by AES-256 bit key encryption. Our latest SSL scan report from Qualys Inc (leader in compliance and auditing) gives MockFlow: A+ rating as shown above.
Application Security
Security at the application level is important to prevent attacks like SQL injection, XSS from hackers. At MockFlow we have taken various steps to ensure our application is always secure against such attacks.
Adequate Content Security Policies
Regular Web application scanning for vulnerabilities
OWASP Top 10 validation
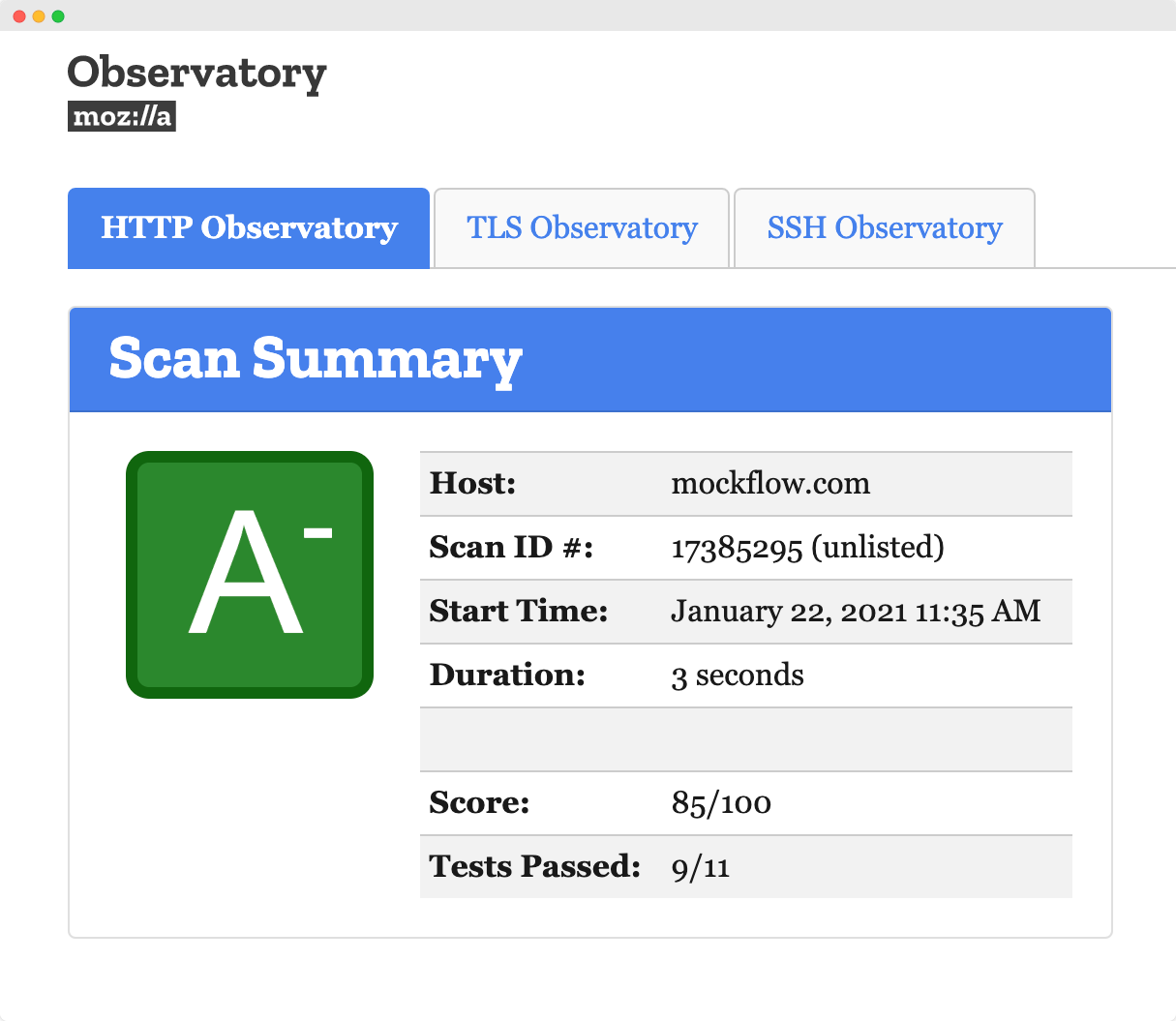
Validation of our security with Qualys Inc and Mozilla observatory
Network vulnerability testing with Qualys Inc. and AWS Detective
Following best security practices for development
Security Features
Function level security in MockFlow helps team admins to ensure their organization follows secure workflows within their teams when using MockFlow
SSO
MockFlow supports popular Single-Sign-On (SSO) identity providers out of box like OneLogin, Okta. Besides them we also support SAML for other providers
Secure Sharing
All projects created in MockFlow are by default private and can be shared with other users using the required permissions - Reviewer, Editor or Admin
Secure Delete
Deleting projects in MockFlow asks for password token to safeguard user data. Also all important user actions are logged for audit purposes.

Encrypted .wire file
Secure offline sharing of .wire design files created with WireframePro desktop app by password protecting them with unbreakable AES-256-bit cipher.
2FA
Two-Factor Authentication
Centrally enable and manage 2FA in admin dashboard for all team members to secure signing-in with a two-step verification process.
Secure Development
This is where it all starts. We always ensure all our organization members undergo security training and follow secure guidelines during coding, testing and deployment.
Code Review
Peer based code reviews are conducted to detect any security faults in code
Security Audits
Application level security scanning is done with Qualys Inc. for detecting any security holes
Security vetting of our vendors
We ensure not only our infrastructure but also the third-party libraries used are updated with latest security patches
Stage based testing
Stage based testing - branch, integration and deployment level helps to catch bugs that might otherwise go undetected
Personal security
Our development center is provided with adequate active and passive security arrangements such as CCTV, user activity monitoring, anti-virus etc...